AI Collapses Cyber Response Window as Attackers Automate Reconnaissance at Scale
Security experts warn that artificial intelligence has eliminated the detection buffer organizations once relied on, with attackers now exploiting vulnerabilities the moment they surface.
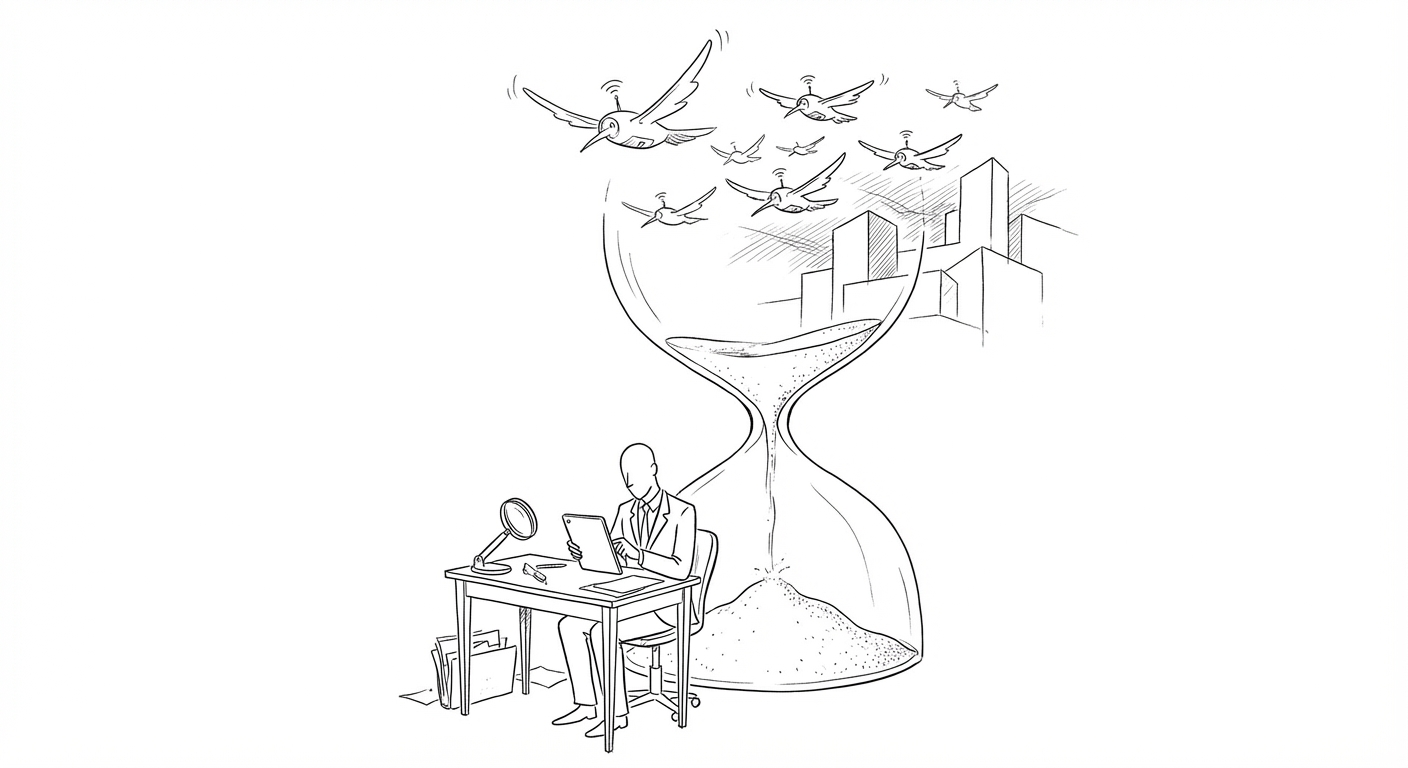
Artificial intelligence has fundamentally altered the tempo of cybercrime, compressing the window between vulnerability disclosure and exploitation to near zero. Security researchers now describe a threat landscape in which attackers maintain continuous, automated surveillance of potential targets, ready to strike the instant a weakness appears.
"There's zero time now," said Aamir Lakhani, Global Director of Threat Intelligence at Fortinet, describing how AI enables reconnaissance and exploitation at global scale. The shift marks a departure from traditional attack patterns: adversaries are reducing noisy activities such as brute-force attempts while increasing successful exploitation, making intrusions harder to detect before damage occurs.
The acceleration represents a structural change in the balance between offense and defense. Where organizations previously counted on days or weeks to patch systems after a vulnerability became public, that buffer has evaporated. Attackers now deploy machine learning to index targets continuously, automating the labor-intensive work of mapping networks and identifying entry points.
(Lakhani advises organizations including the World Economic Forum, MITRE, and the Cyber Threat Alliance, focusing on adversarial AI and evaluating how AI systems fail under operational conditions to improve secure-by-design implementations.)
The development arrives as enterprises struggle to match the speed of AI-enabled threats with defensive capabilities. Traditional security operations centers, built around human analysts reviewing alerts, face mounting pressure to adopt automated response systems. Yet the same AI tools that empower attackers also introduce new risks when deployed defensively, including false positives and adversarial manipulation.
Security vendors have responded by integrating AI into threat detection platforms, but the arms race favors attackers who operate without regulatory constraints or accuracy requirements. The asymmetry has prompted calls for rethinking incident response architectures, with some experts advocating for assumption-of-breach models that prioritize containment over prevention.
Keywords
Sources
https://www.darkreading.com/threat-intelligence/ai-is-eliminating-the-window-to-respond-to-cyberattacks
Focuses on Fortinet expert's warning that AI has reduced response time to zero through continuous target indexing and automated reconnaissance.
https://qz.com/aem-ceo-megan-tanel-state-of-agriculture
Brief mention that AI is reaching battlefield applications before consumer adoption, suggesting military-grade threat acceleration.
https://qz.com/holganix-howard-buffett-agriculture-survival
References AI deployment in operational contexts, highlighting speed of adoption in high-stakes environments.
http://markets.chroniclejournal.com/chroniclejournal/article/finterra-2026-4-2-the-trillion-dollar-treatment-a-deep-dive-into-eli-lilly-and-company-lly
Notes pharmaceutical industry's use of AI partnerships to accelerate R&D cycles, illustrating broader automation trend across sectors.
